by CDO Technology Content | Jun 17, 2018 | CDO Technology News, Maintenance, Managed IT Services
We all seem to be in a constant online battle to protect our data from hackers. Without the proper protection, you are at risk every time you go online. Finding the right company to help educate you and protect your business may seem hard to find, but that’s where we come in. CDO Technology of Greenville has a dedicated team that can help you out no matter where you live. We are ready to provide you the highest quality support backed up by 20 years of experience.

CDO Technology can help with Remote IT Support. Call us today for assistance!
CDO Technology provides Remote IT Support to solve your problems. This means that even if you are out of state, we can help with all your computer issues. We have technicians available to help you through your issues and to provide quick solutions. Remote Tech Support can do Computer Optimization, Software Support, Windows Support, Computer Security Support, Virus, Malware, Spyware, and Adware Removal and many, many other types of assistance and computer problem diagnosis.
Remote IT Support is safe and secure. Once you allow us to connect, we log onto your computer using a 256-bit encrypted online connection between your computer and the Remote Tech’s computer. So, no one else can view or access your computer during this session. Only you can initiate this Remote Support Session and you can end the session at any time by closing the support windows on your desktop. Everything CDO does can be seen on your monitor the entire time and you can over-ride the Remote Tech’s work by simply moving your mouse. And CDO CANNOT log onto your computer after the session is over unless you request service again and give us access permission.
CDO’s Remote IT Support is a great option for busy business people to get your computer problems solved painlessly and quickly. Sometimes visiting a computer store can be time consuming, especially if you live far away. We understand fully that you are busy, and we want to respect the urgency of your needs. If needed, our team can remotely access your computer to walk you through the process and do the proper fixes without you having to move a mouse. It’s simple, easy, and secure when you have trustworthy experts helping you.
Contact CDO Technology today to learn more about Remote IT Support.

by CDO Technology Content | Jun 13, 2018 | CDO Technology News, Maintenance, Managed IT Services
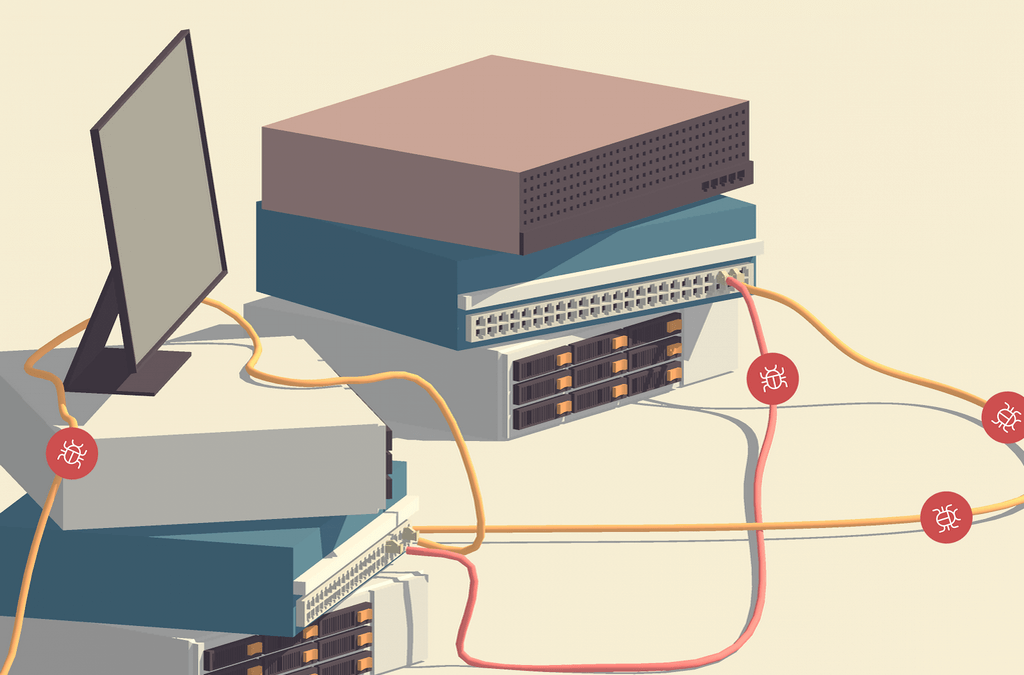
The online world today is more dangerous than ever. Business and personal computers are susceptible to being attacked. Hackers can steal your most valuable data or encrypt it. And if your data gets encrypted, it will prevent you from accessing your files, data, software, and much more. Here at CDO Technology, we understand what it takes to protect your data, and we can explain how it works. We can help bulk up security with enterprise antiviruses, secure your infrastructure with business class routers or firewalls, provide data backups, and much more. A business or enterprise class antivirus isn’t just important, it’s a must. On top of that, our Managed IT Services will catch problems before they become big issues. Once we catch the small problems, we can fix them before they slow down or cripple your business

CDO Technology does managed IT Services in the Greenville area
How do our Managed IT Services work? They do automated updates for MS Windows, MS Office, Microsoft Updates, Java, Adobe, Web Browsers, and more. Managed IT Services will monitor your servers and workstations 24/7. They will also restart the server if an update/patch requires it. Additionally, the automatically clean temporary files, defrag hard drive(s), restart critical services, and install critical patches. The software will automatically notify CDO of problems with performance, services, antivirus, backups, storage, windows log event errors, software changes, and if the server should shut itself off. After an automated notification, CDO will review problem and contact the customer if the problem requires an onsite or remote service call (service fee applies). These automated notifications can be the difference between CDO fixing an issue before it becomes a major problem (no or minimal downtime) and the server going offline, failing, or becoming corrupted for a major downtime event.
Managed IT Services will monitor data or system backups to make sure that they are backing up according to the prescribed backup schedule. However, it is extremely important that you choose backup software that will check the data for corruption and completeness prior to backup, encrypt the data both locally and for transmittal to the Cloud. This will ensure that should you ever need the backup data that it will be available completely in a non-corrupted form. CDO believes that every business should have a local backup (on-premise) and a backup in the Cloud (off-premise).
Business owners need to be educated on what they need to do and how to do it properly and affordably. As these viruses and hackers continue to advance, combating them requires an ongoing and evolving process. It’s not enough to just react, you need procedures and services in place prior to a hack, virus infection, or hardware failure.
Contact CDO Technology to help keep you safe by protecting your business, data, and your future.

by CDO Technology Content | May 16, 2018 | CDO Technology News, Managed IT Services, Security
The current technology market is adapting so quickly that it can be hard to keep up with. In 2017, we had one of the worst data breaches in history when Equifax was hacked and the information of 143 million users including social security numbers was exposed. The most current data breach, and the biggest one experienced to date, is the Data Analytica scandal involving the information of 200 million registered voters on Facebook through a 3rd party app. These data breaches are happening more frequently and affecting more people all the time. Understanding what Fortune 500 companies are doing to keep your information safe from cyber attacks is both critical and very complex.

CDO Technology handles Cyber Security for Greenville, South Carolina
Fortune 500 companies need to stay on high alert because one attack can destroy their reputation, trust of their users and can adversely affect long term profits. Companies must provide constant education and preventative measures for all their employees to help slow down data breaches. This educational process includes learning the latest trends in cyber breaches and learning how to avoid them. This process can be tedious, as phishing scams, remote access, and fake software updates are constant battles between the users and criminals. The trick for users is making sure that we have a good antivirus and strong security hardware at our house or business. We must also be educated on as many possible threats as possible.
As online consumers, people must understand the risks that are involved in giving up personal information. It’s in our best interest to make sure the right security measures are put in place on our computers and that viruses are removed as quickly as possible to prevent any further damage. Before we opt-in online, make sure we understand what we are opting in. We must do more than just read the text provided, we must also understand the source and understand where our personal information will be distributed.
Here are few tips that can help you prevent attacks:
- Be picky with who you share your confidential information. Consider opting out of company’s sharing policies.
- Always keep a good updated antivirus on your computer and have strong security hardware in your home or business to stay ahead of cyber criminals.
- Be aware that these criminals are on social media as well. Make educated choices on what you share and who you share it with.
- Always keep up with updates on your computer as Microsoft and Apple constantly provide security updates to help prevent attacks.
- Always report suspicious emails or content to help the businesses know that there are attacks going on.
I hope that I have provided some general information on what to watch out for and how to protect your personal information. CDO Technology spends a great deal of time researching the latest trends and staying up to date on ransomware, virus protection, and security hardware to make sure that you have an ally online.
If you believe that your computer and your personal information is at risk, we can help you get the antivirus and security hardware to stay protected. Contact us today to learn more about cyber security.
by CDO Technolgy | Jan 10, 2018 | CDO Technology News, Managed IT Services, Networking
5 Tips for Protecting Your Small Business from Cyber-Hackers
1) Commercial Grade Antivirus
Gone are the days when free, downloadable antivirus software could keep your business safe from outside threats. In our new age of increasing cyber vulnerability, you need hardy software to protect the business you’ve worked so hard to grow.
While there are many free antivirus software options, they all share some common, massive vulnerabilities: features and updates. Free software lacks the range of features that protect you from different infection sources: email, web, network, etc. Plus, many only update once per week, and there’s a whole slew of malicious things that can happen between these updates. Business grade antiviruses update several times a day, and they are much more complete and secure. Even better, most only cost about $35 per device per year!
This is one area where you can’t afford to opt for the free version. With devastating viruses like WannaCry! becoming more and more common, the primary line of defense for small businesses is a strong antivirus.
2) VPN Routers or Firewall Appliances
Handling sensitive records and client information? Need an actually secure way to remote in from home to your business computers? If so, a VPN Routers or Firewall Appliances are a must.
Firewall appliances keep connections safe and secure from hacking and other cyber-attacks. Is your business HIPPA compliant? HIPPA compliant firewall routers are even more secure and they are required if your business falls under HIPPA standards.
Lastly, VPN Routers or Firewall Appliances give you the ability to securely remote in to your business computers from home. Don’t feel like going into the office? Or, need to access sensitive client information while you’re on a business trip? VPN and firewall routers make it safe to access your business data from anywhere.
3) Regular Maintenance and Updates
For some, this is a no-brainer. For others, it simply never happens. Whichever category you fall into, it can still be challenging to keep regular, scheduled maintenance and updates a priority. Regardless, doing regular maintenance on your business computers and network is critical to maintaining your security, fast access to data, and a trouble-free work experience.
Regular software updates for Windows, Java, Antiviruses and other software help keep your computers safe and secure. Just as important, backups should be checked routinely to make sure they are working properly. There is nothing that can ruin your day like needing to retrieve a backup to find out it is not there, incomplete, or corrupted.
This is by far the easiest security component to neglect, but it is also one of the most dangerous. Which is why, for many, it is extremely prudent to hire someone to do it for you. An IT company can help enormously by using automated remote monitoring software. This will guarantee that updates are routinely done and hard drives/data backups are monitored for defects so they can be replaced before they fail and you lose critical data.
Are you in the Carolinas? CDO Technologies provides just these services for local businesses. Learn more here.
4) Trusted Back-Ups
If you have data that is critical to the daily operation of your business, you know how scary the thought of losing that data is. Accordingly, it is essential that you have consistent backups you can trust.
To insure against the worst, you need an on-premise backup and a Cloud backup. The on-premise backup allows you to quickly retrieve critical information if your computer or server’s hard drives die, files are damaged, or files and folders are lost.
On the other hand, the Cloud backup allows you retrieve your critical data if the worst happens. Your office could be flooded or a fire could destroy the computer or server that critical data is on. Somebody could steal the computer or backup that has critical data on it or a nasty virus could infect all your office’s hard drives/backups with critical data on them. These scenarios may sound farfetched, but they happen to businesses every day. Cloud Backups store older versions of the backup (perhaps only days before the infection) that have not been infected yet. Using Cloud backups, you can reset to happier times and get back to work.
5) Annual Network Evaluation
Five years ago, you invested in new network infrastructure. At first everything worked great, but slowly you began demanding more. As the number of employees grew, new and beefier software was added to your daily business operations. You asked for your IT infrastructure to do more and different types of work with the same equipment. And, finally, the obsolescence of your (now dated) computers, network equipment, and servers set in and caused slowness, lockups, and employee aggravation.
The tech world is moving faster every day, and you are responsible for keeping up. Your network infrastructure has to be maintained and eventually upgraded to keep up with a growing business. Otherwise, you will inevitably fall in a tangled heap of inefficiencies, security holes, frustration, and pain.
To protect against this failure, get your network evaluated annually by IT professionals.
Are you in the Carolinas? CDO Technologies provides just these services for local businesses. Learn more here.
by CDO Technolgy | May 6, 2015 | CDO Technology News, Maintenance, Managed IT Services
Perhaps one of the most frustrating malware infections found today is file encryption ransomware. The two notable ones are CryptoLocker and CryptoWall. These are classified as malware; they are not technically viruses. Ransomware often infect a computer by being downloaded in a seemingly harmless file. They then encrypt one’s personal data and demand payment in exchange for a decryption key that is stored on a remote server. There is deadline by which payment must be received before the key is deleted; after which, access to the encrypted data is impossible.
Initially it is important to have a basic understanding how one is infected and how ransomware works. Both CryptoLocker and CryptoWall need to be downloaded, and are most commonly received as email attachments; although, they can also be downloaded from websites. These websites are often advertising or media sharing sites. To be infected the file need only be downloaded; it does not need to be opened. The infected files in email attachments often appear as zipped files, but these too need only be downloaded. Once downloaded, the malware uses an asymmetrical algorithm design to generate encryption keys. This means there two keys. One is called the public key which is used to encrypt files, and the other is called the private key which is used to decrypt files. The private key is stored on a remote server controlled by the attacker. It is notable that CryptoLocker and CryptoWall do not lock users out of their computers, as is the case with many other kinds of ransomware. They only encrypt data files.
The Crypto ransomwares usually have a list of file types that it searches for to encrypt. These are primarily different formats of image and text files. Depending on the malware sometimes music is encrypted, and a new version of CryptoWall targets game files. Both CryptoLocker and CryptoWall are aggressive and can infect baked up files on external hard drives and network devices when they are connected to the infected computer and turned on. Some ransomware also sends itself to other people via email from the originally infected computer. When access to an encrypted file is attempted by the owner, a message will be given informing the customer that they need to pay a specific amount of money within a certain period of time to get the private key and gives instructions on how to make payment. Typically 72 hours is the period of time given, but in some cases it will give the owner a few weeks and the cost will rise every week. Both CryptoLocker and CryptoWall usually display a countdown timer with the message. The amount of money asked for is usually around $300 to $500. In certain cases, people have been charged up to around $1000. Some versions of ransomware, especially in the case of CryptoWall, ask for payment in bitcoin. Bitcoin is an unregulated digital currency that can be mined (process of creating new bitcoins) and can be used in certain transactions and exchanged for other currency. Sometimes payment is required through cash card or prepaid credit card because such cards are untraceable. When the specified period of time passes and if payment has not been made, the private key is deleted from the remote server and the owner can never access their files again.
Although very similar, there are some small differences between CryptoLocker and CryptoWall. It is important to note that CryptoLocker is older than its counterpart and is currently rarer. An international, joint law enforcement operation shut down the majority of servers that were being utilized to distribute CryptoLocker when they took out the Gameover Zeus botnet. Additionally, CryptoLocker has been reverse engineered and many private keys have been recovered giving those infected some hope. There are also still several copycat versions of CryptoLocker in circulation; although few neither are as sophisticated nor do these have any design improvements over the original malware.
CryptoWall became more prominent after the demise of CryptoLocker. CryptoWall infects computers in much same way as CryptoLocker; although, it utilizes weaknesses in websites and employs exploit kits to infect users. It can also be contracted in downloads and emails. As before mentioned, CryptoWall demands only bitcoin as payment and typically charges a higher base amount than CryptoLocker. CryptoWall usually provides a website through which infected people can pay. This website is designed to make tracing difficult. CryptoWall is not yet as widespread as CryptoLocker. The primary concern with CryptoWall is that there is no way to recover the files it encrypts without paying the criminals behind it. CryptoWall can always be removed, but documents and images will remain encrypted.
There are some simple but important ways to reduce the risk of infection. The first order of business is to maintain a good anti-virus on one’s computer. Additional tools that target malware are also helpful to keep the system clean. Backing up all of one’s user data, especially text and picture files, is essential. External hard drives and similar devices should be turned off or disconnected from the computer when not in use. This is important because, after the computer is infected, ransomware can easily infect any connected data storage device(s). Caution should be used when surfing the internet and when checking email. Any program or file that is downloaded from the internet should come from the original source, and third party download sites should be avoided. If an email is received that is not recognizable, do not download any attachments from it. All these guidelines are helpful for general protection, as well as ransomware.
CryptoWall is definitely more feared because it is the only ransom malware from which your files cannot be saved if you chose not to pay for the private key. However, the majority of other ransomwares can all be removed without data loss. CryptoLocker is much less of a threat since its downfall; although, it can still cause significant harm as can its copy cat counterparts. Caution and regular backup of files are the two most important pillars to avoid the frustration that encryption ransomware presents.

by CDO Technolgy | Aug 30, 2014 | Business Servers, CDO Technology News, Managed IT Services
What are Servers?
Servers have been around as long as networks. The generic use of a server is to ‘serve’ something to other computers. This communication is done with a variety of different server types with their own specific uses. They act as facilitators, storage, and so on. Not all server types are exclusive; many types can be simultaneously in use on the same server machine. Some servers can even be client computers (those on which people access the data being served) at the same time.
Some common types of servers are most recognizable. These are: FTP, proxy, game, and web servers. These machines are usually somewhat similar to the personal computers found in most homes and businesses, although they usually have specific software and hardware to provide a smoother transition of the data. Servers usually have more storage space, faster processors, and more RAM (random access memory) in order to make them more efficient. Rather than a standard operating system used by the general public (such as Windows 7), servers usually have a server platform. An example of this for a PC would be Microsoft Server.
FTP servers are used to provide access to files, either publicly or after using a login, depending on whether the files are free or for a fee. This functionality is usually included on web servers, as well, to allow easy access to web site owners to upload and download their own files.
Proxy servers are an extra step between the end user (also known as the client computer) and another server (usually a web server) that handles filtering, sharing connections, and helps to improve performance. These are sometimes used by employers to limit employees’ access to certain web sites from the workplace.
Game servers are those used by online games to provide the interface and processing for them. These are most notable when the game is an MMO (massive multiplayer online) game, in which many people around the world are connecting at the same time, to play the same game. There is often interaction between the players, which necessitates a server that is powerful enough to keep up without causing lag (pauses in the gameplay, during which the game continues, but the player misses the action because the server ‘catches them up’ by skipping).
Web servers are by far the most common ones. These are the servers that house the web pages (such as the one you are currently reading). These communicate with the client’s browser and send the information – text, images, videos, etc. – that is requested. Pretty much anything that is accessed through a browser (such as Internet Explorer, Firefox, Chrome, etc.) is processed by a web server.
Others include application servers, which handle linking databases with web servers; list servers, which handle mailing lists for newsletters and other bulk email processes; chat and IRC (internet relay chat) servers, which allow real-time communication between people wherever they are; mail servers which handle basic email; and news servers which carry newsgroups such as the USENET service, although these are not as popular among the general public as they once were.